ThreatLocker
Zero Trust – Unfortunately in the World of IT we have now moved into a World where we can trust no one! Unlike traditional antivirus programs, Application Control from ThreatLocker® gives you complete mastery over your endpoints.
Unlike other antivirus, Application Whitelisting puts you in control over what software, scripts, executables, and libraries can run on your endpoints and servers. This “default deny” approach not only stops malicious software, but it also stops any other unpermitted applications from running. ThreatLocker® is the Gold Standard from Viruses, Ransomware and other malicious software but it also stops any other unpermitted applications from running.
ThreatLocker® protects against every kind of malware that traditional antivirus programs do, but we go much further. Many kinds of cyberattacks are resistant or immune to antivirus, but not ThreatLocker®.
- Zero-Day Attacks: ThreatLocker® protects against vulnerabilities that haven’t even been discovered yet
- Macro Viruses: Malware embedded in trusted programs like Office can’t overcome ThreatLocker®’s Ringfencing™
- Fileless Malware: Even malware that hides in memory can’t sneak in; if its code isn’t on the trusted list, it isn’t getting access
- Ransomware: Ringfencing™ lets you dictate how apps interact with data; if a program, ANY program, tries to encrypt data it isn’t authorized to, it will be blocked
ThreatLocker® not only lets you track and control external data access (e.g., via the internet), but internal access as well. When your security team has complete visibility over your data storage, they will be able to block data theft before it happens.
-
- Track Permission Changes: If a user grants access to someone they should not have whether intentionally or not, you’ll know immediately
-
- Control Physical Copying: With the right ThreatLocker® Storage Control policies in place, a bad actor on your premises with a USB drive won’t be able to copy a thing
-
- Monitor Access: See who is accessing your files and when with detailed reports generated in real time by ThreatLocker®
- Restrict Applications: Let only trusted apps access your data, as determined by your custom policies
What is ThreatLocker Ops?
ThreatLocker Ops harnesses the power of the ThreatLocker® community in a new way to combat and mitigate cyber threats. With the help of ThreatLocker’s policy-driven solutions, newly added data collection modules, and data points, ThreatLocker Ops adds the benefits of alerts and detection while keeping your stack proactive.
ThreatLocker Ops extends ThreatLocker’s zero trust platform to not only block and prevent threats but also monitors behaviors occurring within your environment, so you can respond to attempted breaches. This helps IT professionals stay ahead of exploits of both known and unknown vulnerabilities while ensuring that threats are blocked by ThreatLocker®.
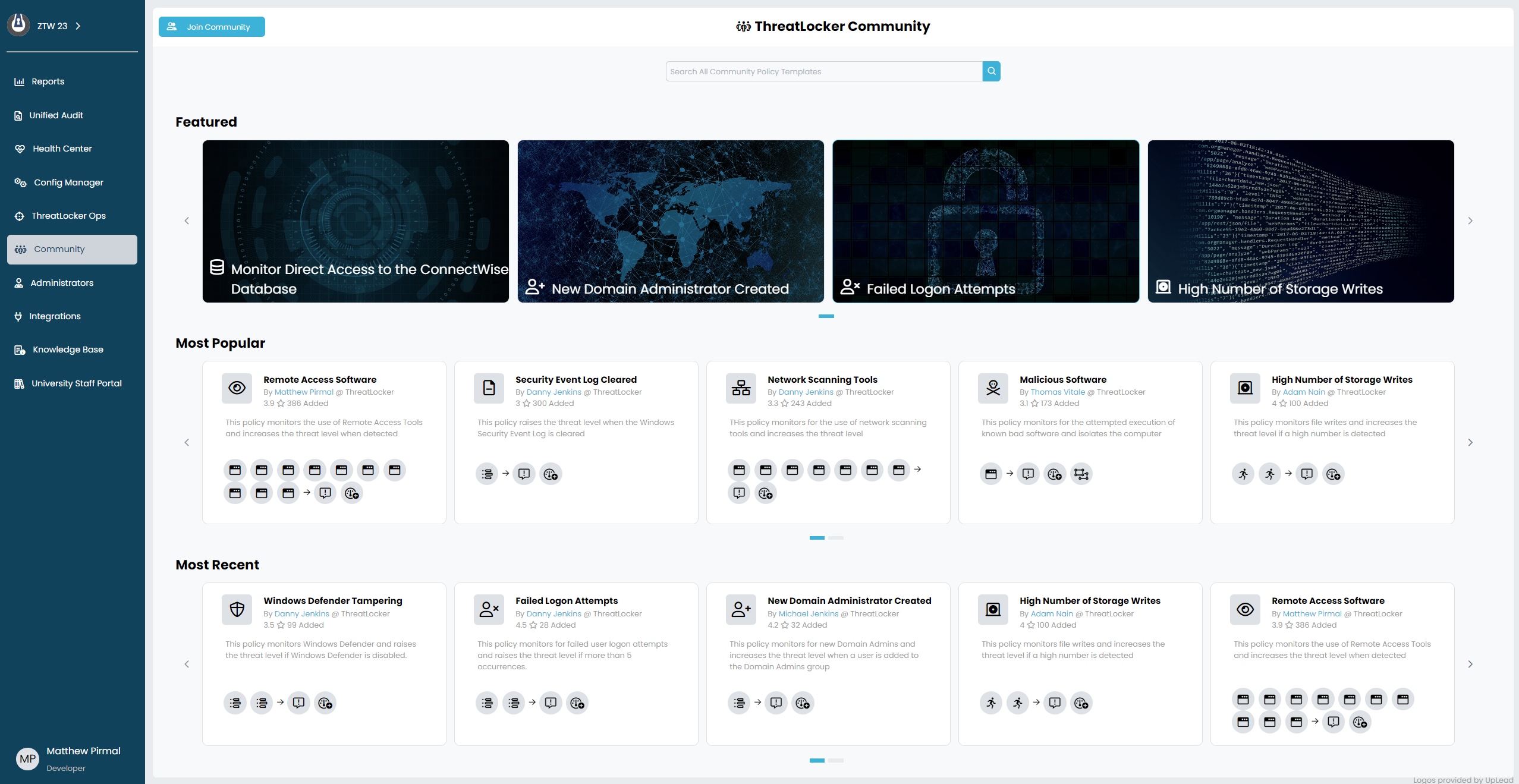
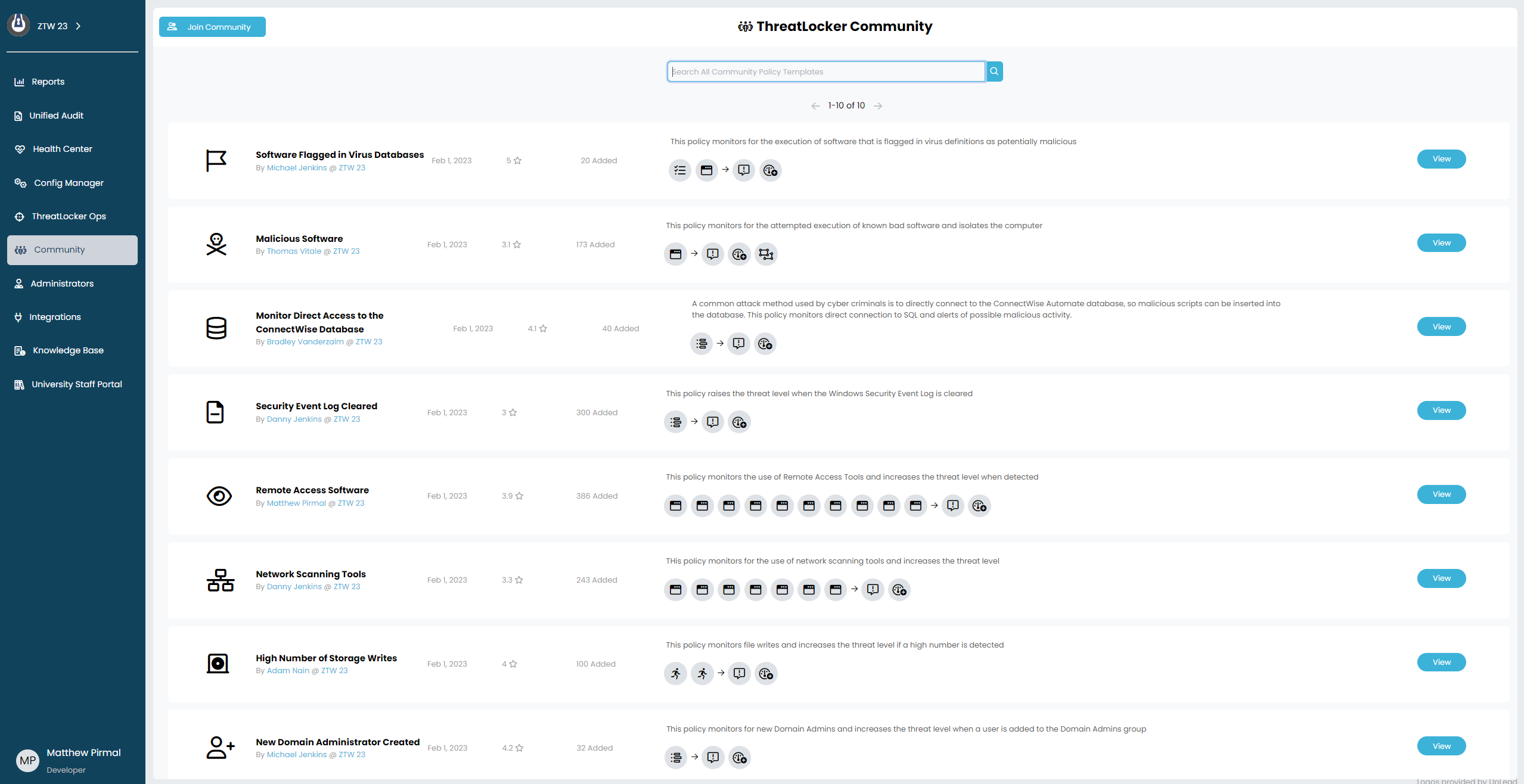
Why ThreatLocker Ops?
ThreatLocker Ops allows organizations to work together with the common goal of stopping threat actors. By sharing policies that are relevant to other organizations, IT admins can continue enhancing their security stack and create successful policies developed by community members with feedback to better improve your overall defenses. Ransomware gangs work as teams to infiltrate and harm your organization, ThreatLocker Ops is the key to constructing your own team and staying two steps ahead of ransomware groups and their malicious agendas.
How Does it Work?
ThreatLocker Ops monitors behaviour patterns of software with the addition of detection and alerts through event logging. This feature allows IT systems to be aware of what’s going on within their environment without needing to respond or react because the application would already be blocked.



